Wanna Decrypter 2.0 ransomware attack: what you need to know
By Bill Brenner as written on nakedsecurity.sophos.com
Updates as of 05/15/2017:
-
Multiple news reports have focused on how this attack was launched using NSA code leaked by a group of hackers known as the Shadow Brokers. That’s certainly what seems to have happened based on SophosLabs’ own investigation. A more detailed report on that is planned for early next week.
-
Sophos will continue to update its Knowledge Base Article (KBA) for customers as events unfold. Several updates were added today, and are summarized below in the “More guidance from Sophos” section.
-
Microsoft took the highly unusual step of making a security update for platforms in custom support (such as Windows XP) available to everyone. The software giant said in a statement: “We know some of our customers are running versions of Windows that no longer receive mainstream support. That means those customers will not have received the Security Update released in March. Given the potential impact to customers and their businesses, we made the decision to make the Security Update for platforms in custom support only, Windows XP, Windows 8, and Windows Server 2003, broadly available for download here.”
-
With the code behind Friday’s attack in the wild, we should expect copycats to cook up their own campaigns in the coming days to capitalize on the money-making opportunity in front of them, said Dave Kennedy, CEO and founder of information security consultancy TrustedSec.
-
The attack could have been worse, if not for an accidental discovery from a researcher using the Twitter handle @MalwareTechBlog, who found a kill switch of sorts hidden in the code. The researcher posted a detailed account of his findings here. In the post, he wrote: “One thing that is very important to note is our sinkholing only stops this sample and there is nothing stopping them removing the domain check and trying again, so it’s incredibly important that any unpatched systems are patched as quickly as possible.”
***
It was a difficult Friday for many organizations, thanks to the fast-spreading Wanna Decrypter 2.0 ransomware that started its assault against hospitals across the UK before spilling across the globe.
The attack appears to have exploited a Windows vulnerability Microsoft released a patch for in March. That flaw was in the Windows Server Message Block (SMB) service, which Windows computers use to share files and printers across local networks. Microsoft addressed the issue in its MS17-010 bulletin.
SophosLabs said the ransomware – also known as WannaCry, WCry, WanaCrypt and WanaCrypt0r – encrypted victims’ files and changed the extensions to .wnry, .wcry, .wncry and .wncrypt.
Sophos is protecting customers from the threat, which it now detects as Troj/Ransom-EMG, Mal/Wanna-A, Troj/Wanna-C, and Troj/Wanna-D. Sophos Customers using Intercept X will see this ransomware blocked by CryptoGuard. It has also published a Knowledge Base Article (KBA) for customers.
NHS confirms attack
National Health Service hospitals (NHS) in the UK suffered the brunt of the attack early on, with its phone lines and IT systems being held hostage. NHS Digital posted a statement on its website:
The UK’s National Cyber Security Centre, the Department of Health and NHS England worked Friday to support the affected hospitals, and additional IT systems were taken offline to keep the ransomware from spreading further.
Victims of the attack received the following message:
Find out today if your current system meets today's minimum security recommendations. Call Managed Solution at (800) 208-3617
Continued Reading

May 15, 2017
Azure Gov enables digital transformation | US Veterans Affairs
[vc_row][vc_column][vc_column_text] Azure Gov enables digital transformation | US Veterans Affairs […]
LEARN MORECloud Services Page
Government
May 16, 2017
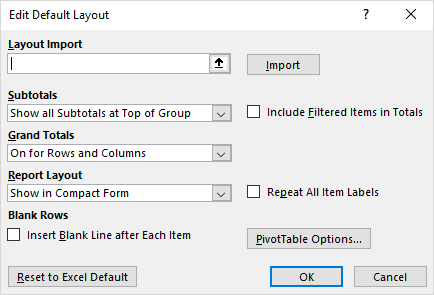
PivotTables just got personal
PivotTables just got personal As written on blogs.office.com As part […]
LEARN MOREOffice365