
Microsoft Dynamics 365 Integration Overview Managed Solution partners with HubSpot […]
LEARN MORE
Managed Solution Earns 2024 Great Place To Work Certification™ San […]
LEARN MORE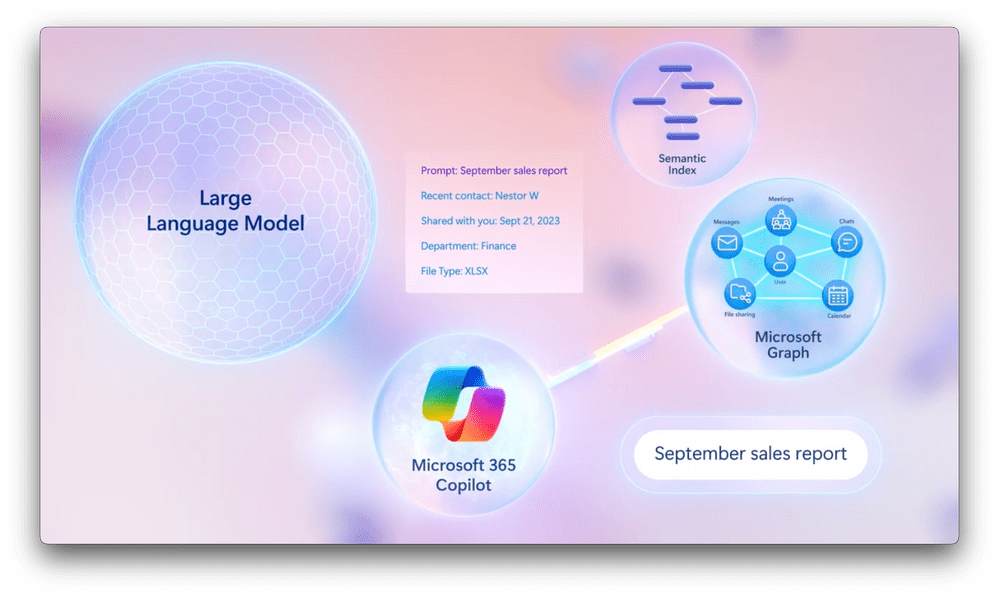
How to Connect External Data with Copilot In the […]
LEARN MORE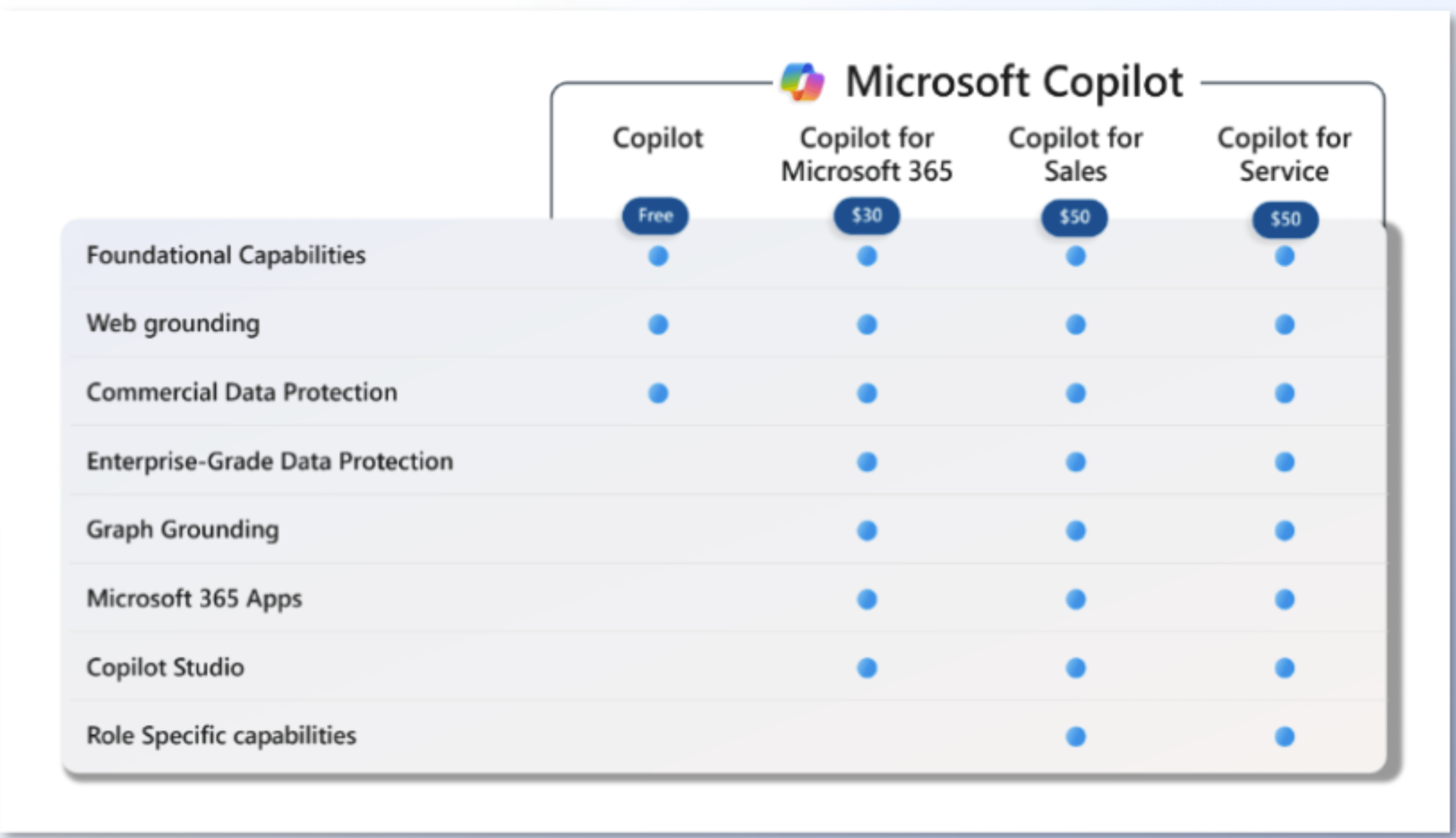
Which Copilot Plan is Right for You? A Guide for […]
LEARN MORE
Fall in Love with ConnectWise Sidekick: Why AI and Managed […]
LEARN MORE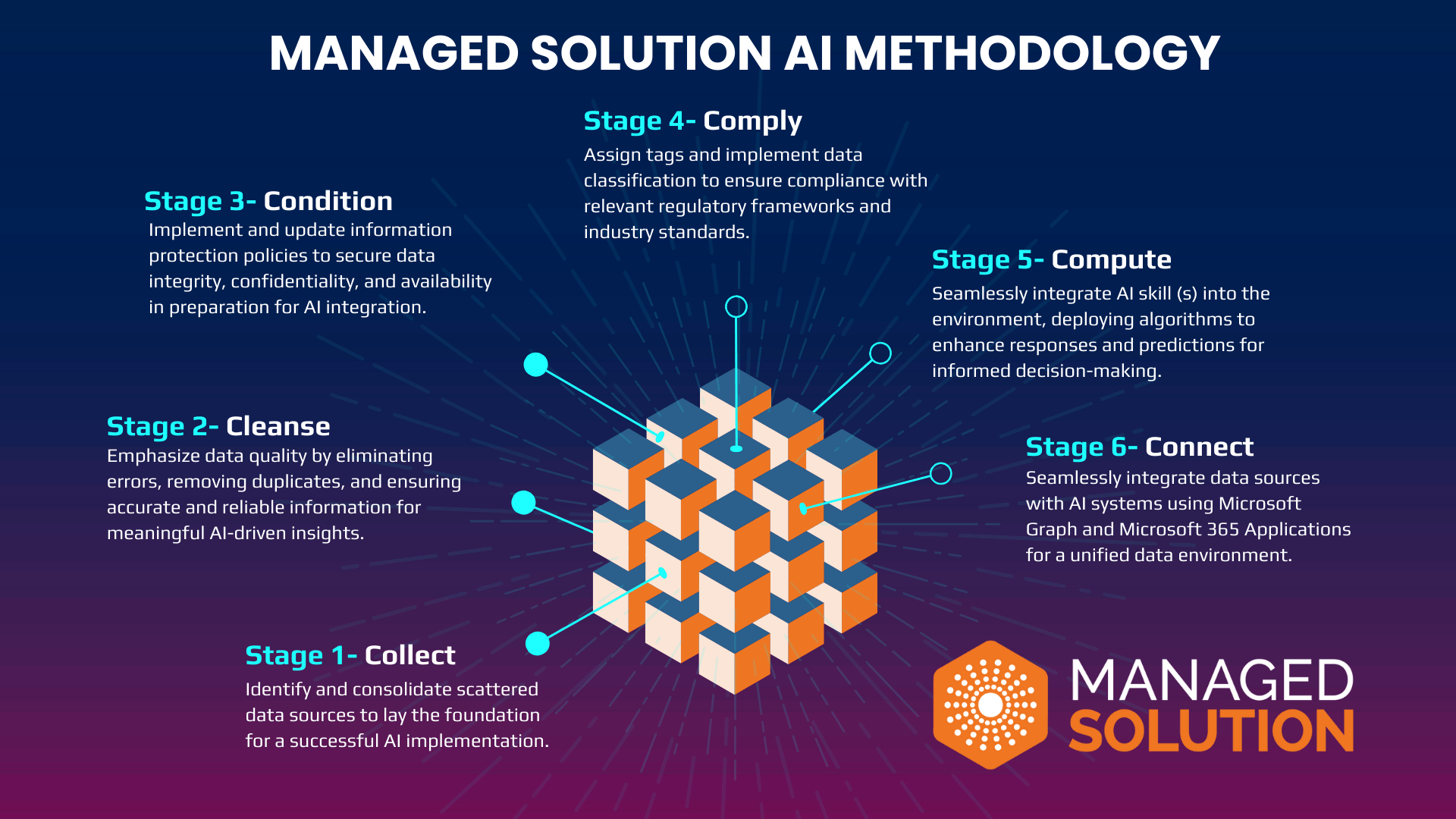
A Six-Stage Methodology for Seamless AI Implementation In today's era […]
LEARN MORE
Expanding Copilot for Microsoft 365 to businesses of all sizes […]
LEARN MORE
The Best New Years Resolutions for IT Departments in […]
LEARN MOREChat with an expert about your business’s technology needs.